Deterministic Snapshot-Bound Control
Commit-gated activation of externally effective computing state
Norcrest develops deterministic, snapshot-bound control primitives for environments where automated outcomes must be reproducible, independently verifiable, and governed by construction.
The core separation is between provisional computational state and externally effective computing state. External visibility and transmissibility remain inhibited until a deterministic publication commit records a state transition in append-only evidence.
External authority is not assumed from execution — it emerges only from a recorded deterministic state transition.
The Problem
Many distributed systems couple execution to dissemination: outputs become externally visible immediately upon generation. In high-trust environments, that coupling produces irreproducible outcomes and weak verification surfaces.
Execution ≠ authority
Externally effective state can emerge without deterministic evidence of a state transition.
Evidence assembled after the fact
Audit trails are reconstructed from fragmented logs and mutable telemetry rather than produced as canonical artefacts.
Non-determinism breaks replay
Heuristic selection, configuration drift, and runtime variance prevent byte-stable reproduction of key identities.
Core Invention
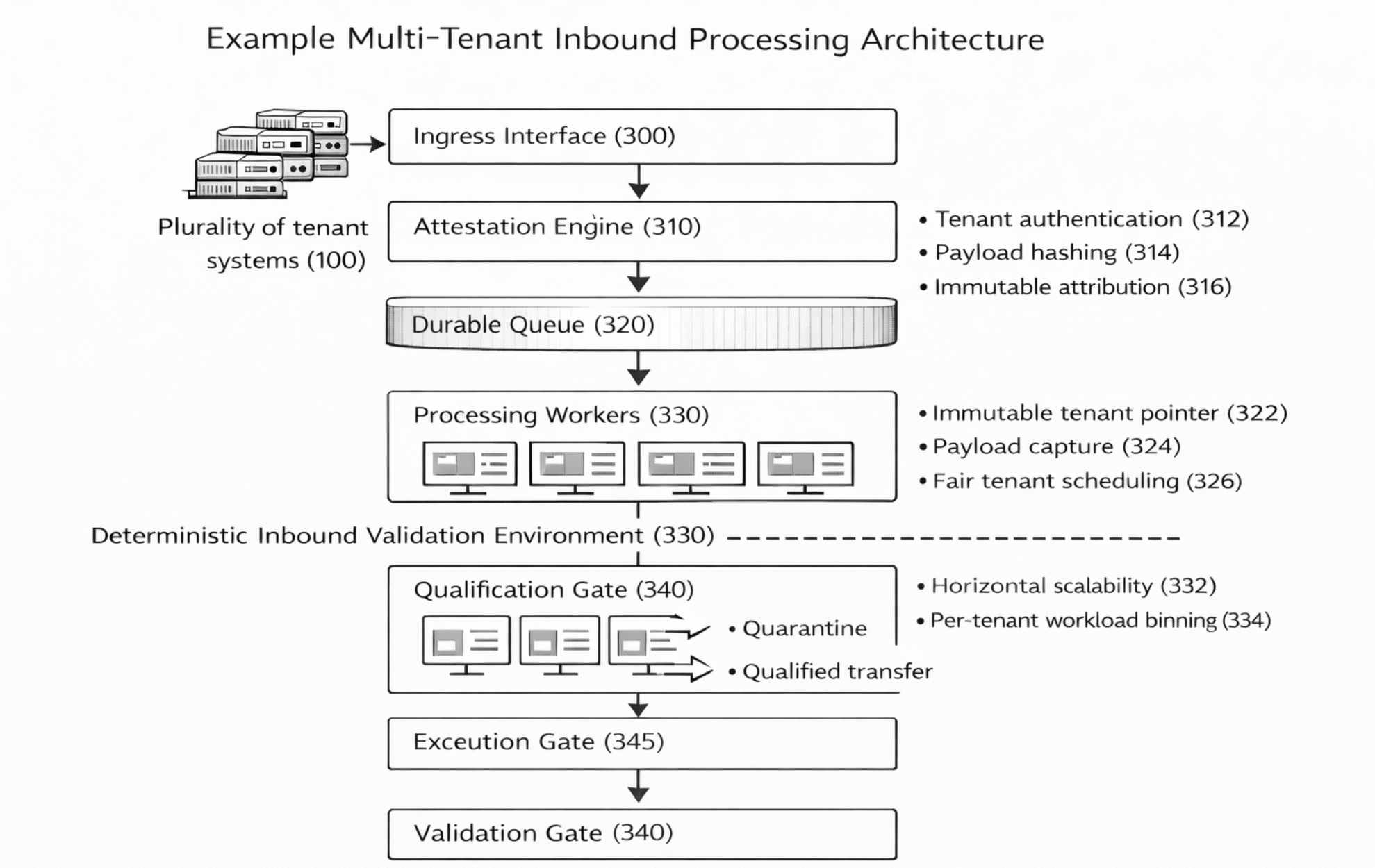
A deterministic, snapshot-bound control primitive in which execution produces a provisional computational state, and externally effective computing state is enabled only after a deterministic publication commit records a state transition with a publication wrapper and publication hash in append-only storage.
Commit-gated activation
External visibility/transmissibility is inhibited prior to publication commit confirmation (fail-closed).
Snapshot-resolved context
Verification binds to an immutable snapshot of registry definitions (policy, schema, routing, constraints).
Hash-addressed evidence
Canonicalisation yields byte-stable artefacts enabling independent recomputation of publication hashes.
Explore
The site is structured as a set of pages matching the core surfaces of the control primitive: problem framing, invention, primitives, verification, and architecture.
Primitives
Snapshot-bound registry context, canonicalisation, publication wrapper + publication hash, transmission inhibition, append-only evidence, export bundles.
Verification
Independent verification by recomputation using canonical artefacts and export bundles.
Research
Publications and collaboration opportunities for independent critique and experimental validation.
